[ad_1]
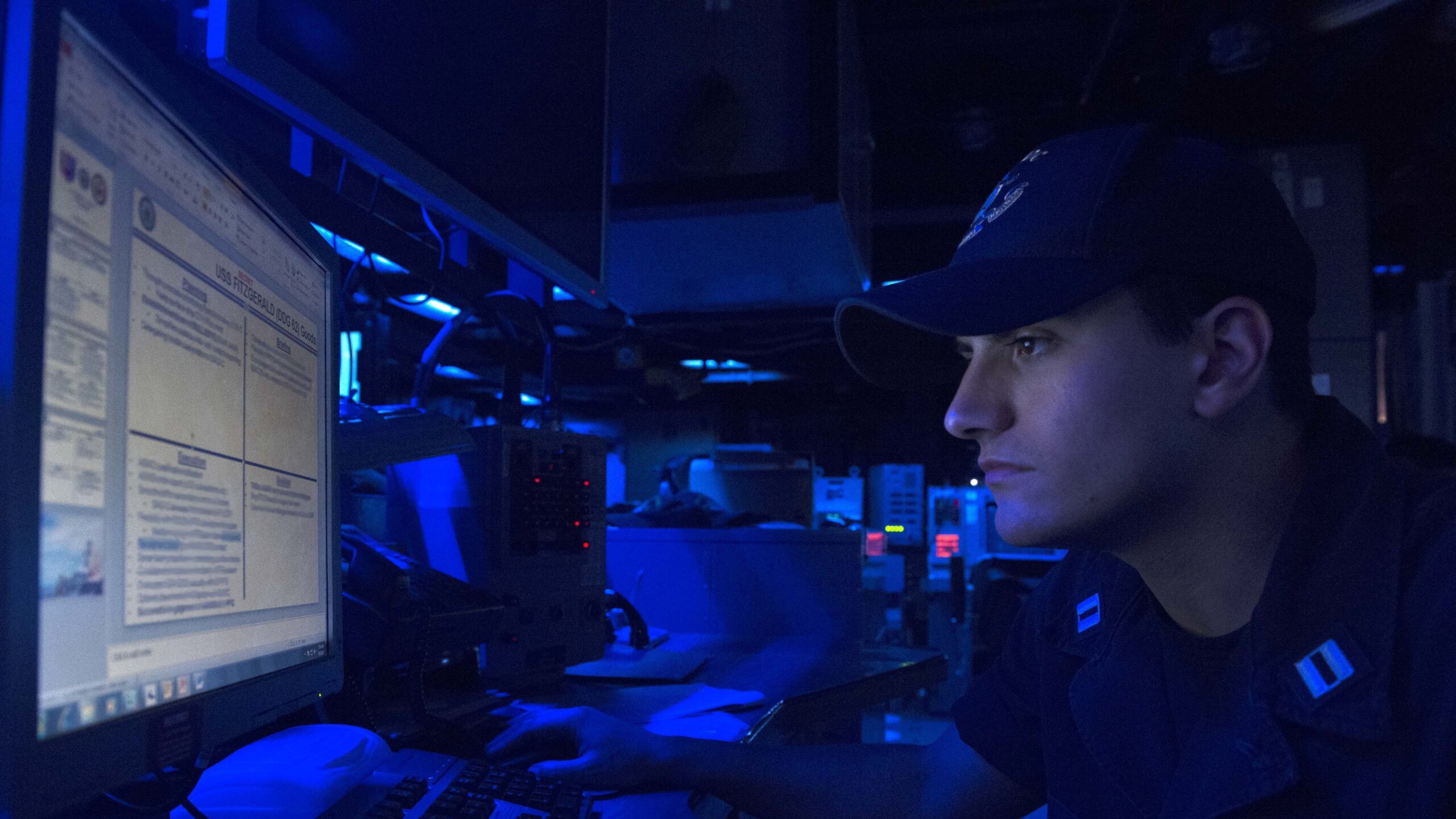
Lt. Christian Asaban sights a laptop observe aboard the forward-deployed Arleigh Burke-course guided-missile destroyer USS Fitzgerald (DDG 62) throughout Multisail 17 on March 8, 2017. (U.S. Navy picture by Mass Communication Expert 2nd Course William McCann/Released)
WASHINGTON: The way the Navy now ways cybersecurity is “wrong,” and the provider demands to transfer from viewing it as a compliance difficulty towards a design rooted in readiness, in accordance to the service’s chief facts officer.
“Today, I would argue that the way that we do cybersecurity at the Section of Navy — and at the Office of Protection but which is higher than my paygrade — … is improper,” Aaron Weis, Navy CIO, reported at the Cloudera Governing administration Forum. “We perspective cybersecurity as a compliance issue. And it is most definitely not a compliance challenge.”
In its place, the support desires to shift toward a readiness product that is measured holistically, he reported.
“And when I speak about readiness, I’m not expressing it is fleet readiness … I’m indicating it is a product encouraged by how we technique readiness,” Aaron Weis, Navy CIO, said at the Cloudera Government Discussion board. “Readiness is some thing that is a dynamic product … It is measured quite holistically.”
Related Distinctive: MS Groups consumers at Army Futures Command possibly uncovered personal data
Cybersecurity via compliance effects in possibility increases, delayed abilities, insufficient safety and squandered assets, in accordance to Weis.
The Navy has been doing the job towards its new, holistic model because past November and to that close made a method known as Cyber Prepared. With the software, the support needs to shift cybersecurity absent from rote compliance paperwork and towards a “cyber ready” condition that permits acquisition speed and superior defends the service’s information and facts.
The system also seeks to “apply types of currency so that we’re not just obtaining an ATO [authorization to operate] once, but you’re continuing to make and re-get paid your ATO daily by way of this concept of currency,” Weis stated.
Associated: App Retail outlet For Warships: Within The Navy’s Task To Revamp How The Fleet Gets Software
In addition to the forex concept, Weis claimed, there are a number of traces of work the Navy is pursuing to move the assistance to a far more holistic cybersecurity technique, such as continous monitoring with software-pushed crimson teaming and vehicle-crimson teaming, acquisition modifications and getting ready its workforce.
“And so we’re on a route. This released final calendar year,” Weis explained. “We are on a first set of sprints, a 90-day sprint, the place we’re putting the meat on the bones of this thought. And we’re also actively performing to determine sets of pilots. And so we’re obtaining a tiny amount of pilots who are volunteering to go by means of this and assist us study and it will be a highly iterative method as we go forward.”
Weir also laid out three broad goals the Navy desires to execute primarily based on its 2019 Cyber Readiness Assessment: modernize the service’s infrastructure, push innovation at speed and defend the service’s details “wherever it is.”
“And notably, we did not use the phrase cyber. I’m of the head that cyber is likely one of the most overused words and phrases in this town, in this market … It usually means every thing to everybody,” he said. “And as a result it sort of signifies nothing at all. So we have to place a finer place on it. We have to defend our information wherever it lives — at relaxation, in transit, in the industrial foundation, in our systems, at the tactical edge. You identify it, we have to be capable to defend it. And we have not been accomplishing a excellent task of that in the earlier as the Cyber Readiness Evaluate articulated.”
Weis’s opinions come as the Pentagon ramps up funding in its cyberspace pursuits and aims to streamline its wide community infrastructure of non-provider-certain organizations.
DoD in its fiscal 2023 ask for needs $11.2 billion to harden its networks, operationalize zero have faith in architecture and boost cybersecurity assistance for defense contractors. The ask for is an $800 million enhance around its FY21 request.
“We’re also investing to strengthen readiness in the nation’s cyber power by funding cyber ranges to help instruction and routines in the cyber area,” Vice Adm. Ron Boxall, director of drive construction, methods and evaluation for the Joint Employees, told reporters March 29. “Finally, the finances lays the foundation for US [Cyber Command] to have ownership of the mission and means of the cyber mission drive commencing in FY24 as directed in the [FY]22 NDAA.”
[ad_2]
Source hyperlink





More Stories
Kellys Blue Book – What is it and Why Use It?
Can You Make Over $100,000 a Year in the Auto Repossession Business?
Be a Backyard Mechanic